© 2024 ALM Global, LLC, All Rights Reserved. Request academic re-use from www.copyright.com. All other uses, submit a request to [email protected]. For more information visit Asset & Logo Licensing.
Error
An error occurred while fetching the data.
Error details: Error: No content found for '/2014/05/19/threat-intelligence-provides-extra-layer-of-networ/' within site 'www.cutimes.com': {"response":{"errors":[{"message":"No content found for '/2014/05/19/threat-intelligence-provides-extra-layer-of-networ/' within site 'www.cutimes.com'","locations":[{"line":1,"column":40}],"path":["articleData"],"extensions":{"classification":"NOT_FOUND"}},{"message":"No content found for '/2014/05/19/threat-intelligence-provides-extra-layer-of-networ/' within site 'www.cutimes.com'","locations":[{"line":99,"column":7}],"path":["youmightlike"],"extensions":{"classification":"NOT_FOUND"}}],"data":{"articleData":null,"articlePackages":[],"youmightlike":null,"readnext":{"contents":[{"uri":"/2024/04/08/learn-how-cu-are-realizing-55-automated-bookings-and-70-instant-funding/","title":"Learn How CU are Realizing 55% Automated Bookings and 70% Instant Funding","prettyDate":"April 08, 2024","kicker":"","image":{"uri":"","width":"","height":""},"primaryCategory":{"name":"","uri":"","channelName":"","channelUri":""}},{"uri":"/2024/04/23/ohio-woman-74-used-a-handgun-to-allegedly-rob-her-own-credit-union/","title":"Ohio Woman, 74, Uses a Handgun to Allegedly Rob Her Own Credit Union","prettyDate":"April 23, 2024","kicker":"News","image":{"uri":"https://images.cutimes.com/contrib/content/uploads/sites/413/2024/04/police-car-e1713899007158.jpg","width":"620","height":"394"},"primaryCategory":{"name":"","uri":"","channelName":"","channelUri":""}},{"uri":"/2024/04/24/callahan-buys-cdfi-consulting-firm/","title":"Callahan Buys CDFI Consulting Firm","prettyDate":"April 24, 2024","kicker":"News","image":{"uri":"https://images.cutimes.com/contrib/content/uploads/sites/413/2024/04/merger-news-e1713962515619.jpg","width":"620","height":"414"},"primaryCategory":{"name":"","uri":"","channelName":"","channelUri":""}},{"uri":"/2024/04/23/new-hires-promotions-revealed-at-6-cus-your-credit-union-partner/","title":"New Hires & Promotions Revealed at 6 CUs, Your Credit Union Partner","prettyDate":"April 23, 2024","kicker":"Career Moves","image":{"uri":"https://images.cutimes.com/contrib/content/uploads/sites/413/2024/02/youre-hired-envelopes-e1707428875637.jpeg","width":"650","height":"433"},"primaryCategory":{"name":"","uri":"","channelName":"","channelUri":""}},{"uri":"/2024/04/23/mortgage-bankers-lower-forecasts-through-2026/","title":"Mortgage Bankers Lower Forecasts Through 2026","prettyDate":"April 23, 2024","kicker":"News","image":{"uri":"https://images.cutimes.com/contrib/content/uploads/sites/413/2022/04/U.S-Economy-e1648835978154.jpeg","width":"620","height":"413"},"primaryCategory":{"name":"","uri":"","channelName":"","channelUri":""}}]}},"extensions":{"DateTime":"2024-04-26T06:54:47.559072133","ResponseTime":"10ms","AuthorizedUser":false,"DebuggingData":"Kangaroo","NavServiceResponse":null},"status":200,"headers":{}},"request":{"query":"query CUTimes__view_article_no_sitedir{articleData:\n getContent(naturalId: \"/2014/05/19/threat-intelligence-provides-extra-layer-of-networ/\", site:\"cutimes.com\") {\n uri\n canonicalUrl\n generatedId\n naturalId\n type\n postFormat\n kickerPresentedBy {\n \t\t label\n \t\t value\n \t\t}\n breadcrumb{\n name\n \t\turi\n }\n presentedBy\n title\n readtime\n timeToRead\n prettyModified\n prettyDateTime\n needToKnow\n byline\n authors {\n name\n description\n imageLarge\n webUrl\n }\n publication\n kicker\n kickerNode {\n name\n slug\n uri\n sectionName\n }\n prettyDate\n prettyDateTime\n pubDate\n modifiedDate\n isDownload\n primaryCategory {\n channelName\n sectionName\n name\n uri\n slug\n channelUri\n }\n tags\n image {\n uri\n width\n height\n alt\n }\n embed1\n embed2\n summary\n categories {\n name\n uri\n channelName\n }\n bodyArray\n slides {\n title\n image\n caption\n height\n width\n }\n\n }\n articlePackages:\n getPackagesForArticle(docId: \"/2014/05/19/threat-intelligence-provides-extra-layer-of-networ/\", limit: 3, publication:\"cutimes.com\") {\n title \n slug\n type \n summary\n cssFile\n navigations {\n name\n link\n }\n articles {\n title\n kicker\n uri\n image {\n uri\n }\n }\n\n \n }\n youmightlike:\n getYouMayLikeForContent(naturalId: \"/2014/05/19/threat-intelligence-provides-extra-layer-of-networ/\", site:\"cutimes.com\") {\n uri\n title\n byline\n prettyDate\n readtime\n image {\n uri\n width\n height\n }\n summary\n }\n readnext:\n getStatsList(site:\"cutimes.com\", topic: \"\", limit: 5, timeframe: \"3days\" ) {\n contents {\n uri\n title\n prettyDate\n kicker\n image {\n uri\n width\n height\n }\n primaryCategory {\n name\n uri\n channelName\n channelUri\n }\n }\n\n }\n }"}}
Go Home

Events
- InsuranceBenefitsPRO Broker Expo 2024April 29, 2024 - AuroraThe premier educational and networking event for employee benefits brokers and agents.More Information
- ConsultingConsulting Leaders in Technology 2024May 16, 2024 - DallasConsulting Magazine recognizes leaders in technology across three categories Leadership, Client Service and Innovation.More Information
- ConsultingConsulting Top Consultants 2024June 27, 2024 - New YorkConsulting Magazine identifies consultants that have the biggest impact on their clients, firms and the profession.More Information
Resource Center
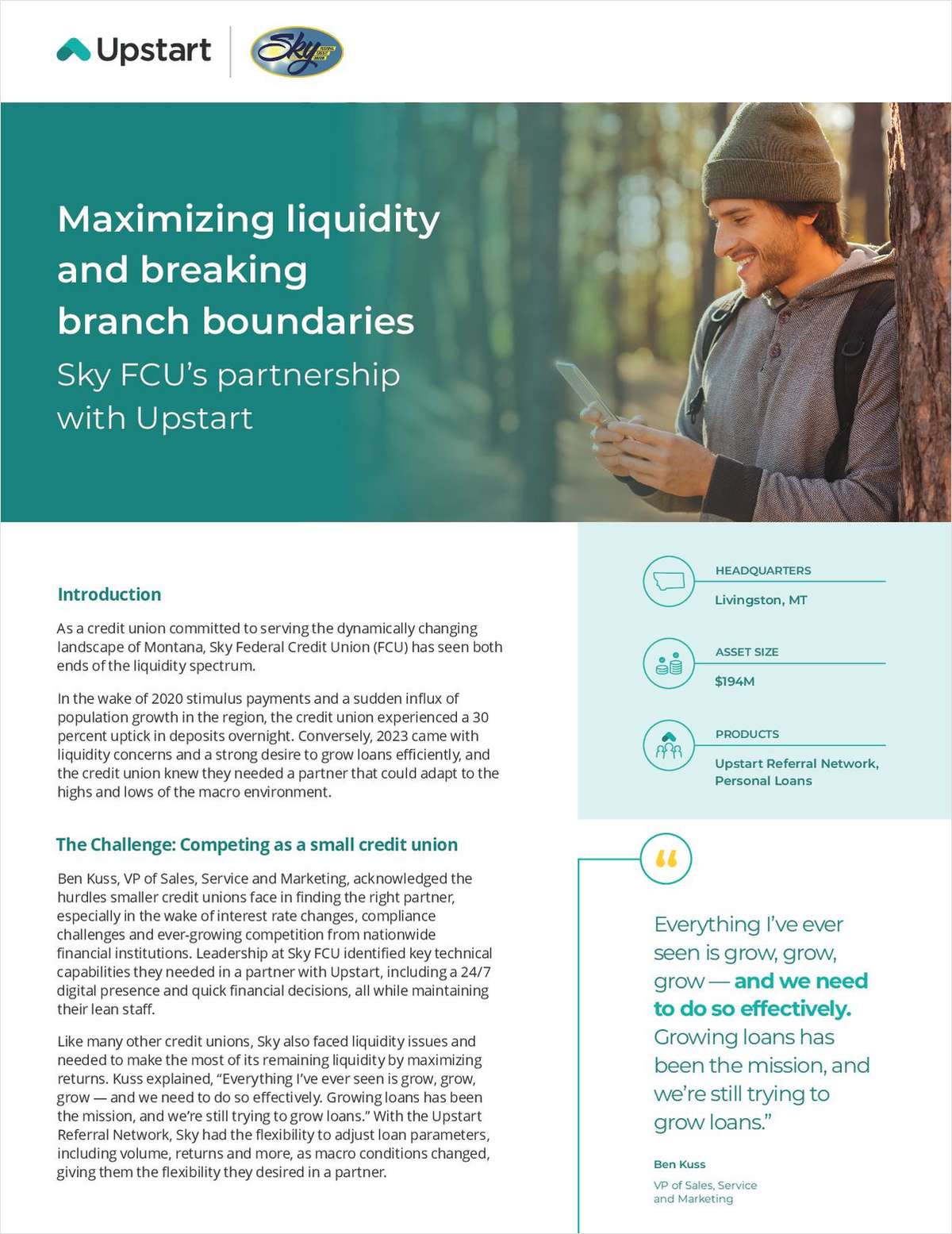
Case Study
Sponsored by Upstart
Maximizing Liquidity and Loan Growth: A Credit Union's Success Story
Uncover the journey of a Montana-based credit union as it navigates economic fluctuations, breaks traditional branch boundaries, and achieves efficient loan growth through a strategic partnership with a cutting-edge financial solution.
White Paper
Sponsored by Melissa
Clean Your Data to Support Member Retention and Growth
Did you know the risk for member turnover drops from 50% to 25% when a member has two or more products with your credit union?² This whitepaper outlines the critical role that clean data plays in helping your credit union retain and grow membership.
White Paper
Sponsored by GLIA
Intelligent Virtual Assistants: One Piece of a Bigger Contact Center Puzzle
When it comes to your credit union’s contact center, Intelligent Virtual Assistants (IVAs) are essential but incomplete solutions for managing volume. Discover how to integrate IVAs into a broader digital member service strategy for maximum efficiency.